The Caesar cipher, also known as the shift or ROT (rotation) cipher, is a simple encryption technique that involves shifting each letter of a message by a fixed number of positions in the alphabet. It is named after Julius Caesar, who is said to have used this method to send secret messages to his generals during wars.
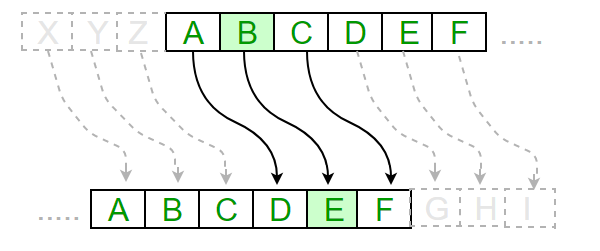
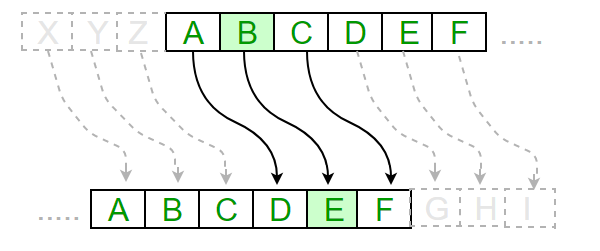
To apply the Caesar cipher, the sender chooses a key (a number between 1 and 25) that determines the amount of shift for each letter. For example, if the key is 3, every letter in the message would be shifted three positions down the alphabet. So, "HELLO" would become "KHOOR" under this cipher.
The ROT13 cipher (Caesar cipher with key 13) is interesting by the fact that the same shift encrypts and decrypts the message (double application returns the original text). Since ROT13 provides virtually no cryptographic security. its last widespread use was to hide spoilers in online forums. Nowadays, it is done with software via CSS and :hover selector. The current main use of ROT13 is to cite it as a canonical example of weak encryption.
The Caesar cipher is easy to understand and implement, but it is also relatively easy to crack through brute force or frequency analysis. Brute force involves trying every possible key until the correct one is found, while frequency analysis takes advantage of the fact that certain letters are more common in a language than others.
Despite its weaknesses, the Caesar cipher is still a useful tool for educational purposes and can serve as a stepping stone to more complex encryption techniques. It has also inspired many variations, such as the Vigenere cipher, which are more difficult to crack.

More information about Caesar cipher
Try Caesar's cipher and ROT variations here!
The Pigpen cipher is a substitution cipher that was used as early as the 18th century. It was often used by Knights Templar and Freemasons to communicate secret messages, but it has also been used by other groups and individuals as a way to hide information.


The cipher uses a grid of symbols, typically consisting of dots, lines, and circles, which represent letters of the alphabet. Each symbol represents a different letter, and the cipher can be easily decrypted if the key to the symbols is known.
To use the Pigpen cipher, the sender first writes their message in plain text. They then substitute each letter inthe message with the corresponding symbol from the cipher grid. The recipient of the message can then use the key to decrypt the message and read it in plain text.

Since the Pigpen cipher is very easy to use and decipher, in modern times it cannot be an effective way to conceal information unless used in combination with other ciphers. It is easily broken with frequency analysis. Nevertheless, it can be a fun and educational tool for teaching cryptography and code-breaking to students.
Try this online Pigpen encoder!
| Feature | Caesar Cipher | Pigpen Cipher |
|---|---|---|
| Type of Cipher | Substitution Cipher | Substitution Cipher |
| History | Used by Romans to encrypt military messages and Caesar's private correspondence | Used by Freemasons and other groups to communicate secret messages |
| Encryption Method | Shifts each letter of the plaintext by a fixed number of positions down the alphabet | Replaces each letter of the plaintext with a corresponding symbol in a grid |
| Key | Single numeric value representing the number of positions to shift | Grid of symbols representing each letter of the alphabet |
| Decryption Method | Shifts each letter of the ciphertext by the opposite number of positions up the alphabet | Replaces each symbol of the ciphertext with a corresponding letter in the grid |
| Security | Can be easily decrypted by trying all possible shifts, or by frequency analysis | Can be easily decrypted if the key to the grid is known, or by frequency analysis |
| Modern Value | Useful for teaching basic cryptography concepts | Useful for teaching basic cryptography concepts |